RKE2 Cluster Direct Kubectl Access
Setup Direct Access to Downstream Cluster
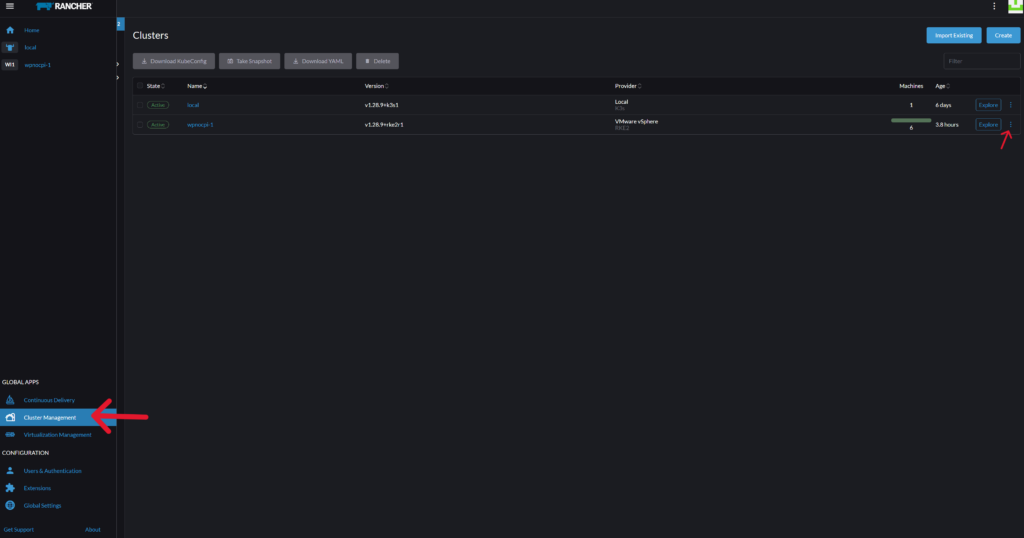
In order to directly access any downstream RKE2 kubernetes cluster (circumventing rancher server), you need to manually enable authorized endpoints using Cluster Managament > Edit Config. However BEFORE doing that, you need to complete the following steps on ALL Control Plane Nodes. You can use MobaxTerm Multi-Execution mode to speed this task up.
Note: For a deep dive on “Authenticating Directly with a Downstream Cluster“ you may visit the official Rancher Labs documentation, here. The instructions on this page are meant to simplify and speed up the process.
Table of Contents
Step 1 – Create a file /var/lib/rancher/rke2/kube-api-authn-webhook.yaml:
touch /var/lib/rancher/rke2/kube-api-authn-webhook.yamlchmod 600 /var/lib/rancher/rke2/kube-api-authn-webhook.yamlnano /var/lib/rancher/rke2/kube-api-authn-webhook.yamlapiVersion: v1
kind: Config
clusters:
- name: Default
cluster:
insecure-skip-tls-verify: true
server: http://127.0.0.1:6440/v1/authenticate
users:
- name: Default
user:
insecure-skip-tls-verify: true
current-context: webhook
contexts:
- name: webhook
context:
user: Default
cluster: DefaultStep 2 – Create config file (create if it doesn’t exist) /etc/rancher/rke2/config.yaml:
echo "kube-apiserver-arg:
- authentication-token-webhook-config-file=/var/lib/rancher/rke2/kube-api-authn-webhook.yaml" > /etc/rancher/rke2/config.yamlCheck config.yaml:
cat /etc/rancher/rke2/config.yamlStep 3 – Restart RKE2 Servers
systemctl stop rke2-serversystemctl start rke2-serversystemctl status rke2-serverStep 4 – Enable Authorized Endpoints via Rancher Server UI
Home > Cluster Management > “kebab” menu > Edit Config
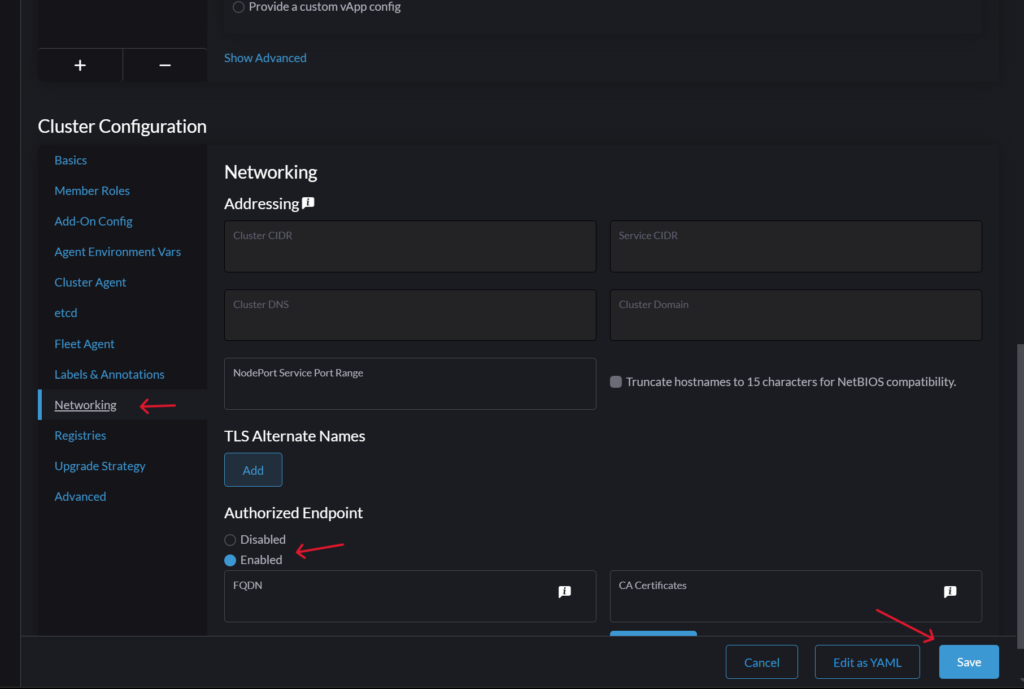
Scroll down to Cluster Configuration > Networking > Authorized Endpoint > Enable
Optional: If you have created an FQDN for your cluster, you can enter it here with a CA Certificate.
Click SAVE to continue. Rancher will apply changes and your cluster will go from “Active” to “Updating”.
Copy New Kubeconfig File
You can now copy the new Kubeconfig file to the path of your choice (example: /root/.kube/kube.config). Just go to Cluster Management > “kebab” menu > Copy KubeConfig to Clipboard.
The kubeconfig file now has contexts that allow you to connect directly to your cluster via one or more of your control-plane nodes. After completing the steps above, your new kubeconfig file will have the same number of contexts plus one “Rancher UI” context (example: 3 control-plane nodes endpoints + 1 Rancher UI endpoint = 4 contexts)
kubectl config get-contexts --kubeconfig /PATH/TO/KUBECONFIG-FILE/config-wpnocpi1.yaml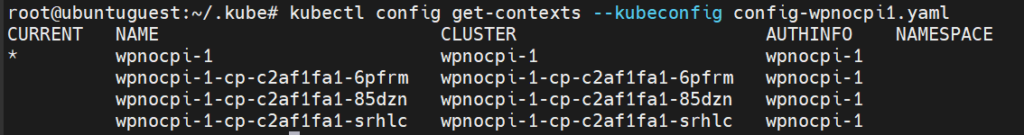
Conclusion
That concludes this RKE2 kubernetes tutorial. You should now be able to directly access your cluster through any of the control planes in your cluster. If you have any questions let me know in the comments below.
READ MORE: Kubernetes





Responses